(Tested on OpnSense 26.1)
When setting up an IPSec tunnel in OpenSense, by default, the tunnel will not be used to to access remote hosts by services running on the firewall host itself (eg. : LDAP for auth, syslog, etc.)
To allow services running on OpenSense to use the tunnel:
- Create a gateway (
System>Gateways>Configuration), bind it to the LAN interface, with the LAN IP as the gateway IP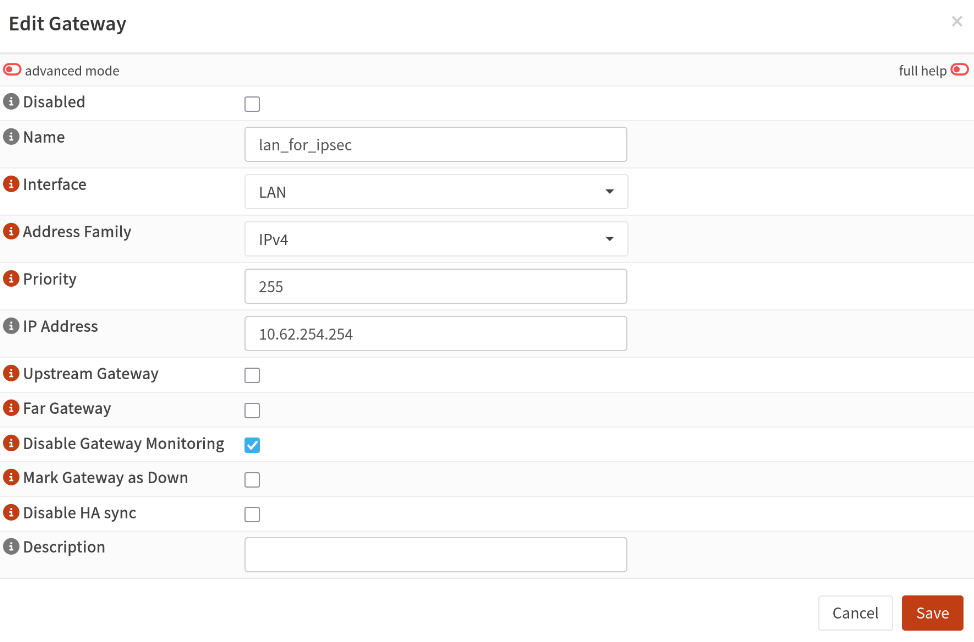
- Create a route (
System>Routes>Configuration) for the remote subnet and bind it to the gateway you just created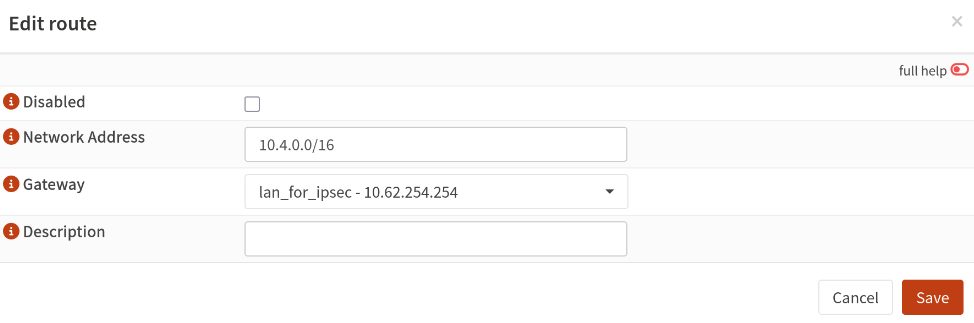
That's it!
]]>